Tech
9253612736: Meaning, Uses & Digital Identity Insights
In today’s interconnected digital world, long numerical strings often appear in communication logs, databases, and online systems without clear context, leaving users curious about their meaning and purpose. One such example is 9253612736, a sequence that may look random at first glance but can represent a structured identifier within telecom systems, verification processes, or data tracking frameworks. As digital infrastructure grows, such numbers increasingly play roles in authentication, routing, analytics, and user identification. Understanding them is essential for recognizing how modern systems operate behind the scenes. In this article, we explore the potential significance of 9253612736, its interpretations, and its broader relevance in today’s data-driven ecosystem.
Understanding 9253612736 in Digital Context
The sequence 9253612736 can be viewed as part of a larger category of numeric identifiers used across telecommunications and digital systems. These identifiers often serve as reference points for routing information, verifying user activity, or tagging system-generated events. While it may resemble a phone number, transaction ID, or tracking code, its true meaning depends entirely on the system in which it appears.
In many cases, such numbers are automatically generated by algorithms designed to ensure uniqueness. This prevents duplication and helps systems differentiate between millions of users or transactions. For example, customer support platforms, mobile networks, and cloud-based databases frequently rely on long numeric strings to manage data efficiently.
When analyzing 9253612736, it is important to consider its environment. If it appears in call logs, it may be linked to telecommunications routing. If found in a database, it could be a primary key or record identifier. In analytics systems, it might represent a session ID used to track user behavior without revealing personal identity.
These numeric patterns are not meant to be interpreted manually by users but rather processed by machines. However, understanding their general purpose helps users become more aware of how digital ecosystems function. In essence, 9253612736 represents how modern systems prioritize structure, uniqueness, and scalability in handling massive volumes of information.
Will You Check This Article: Tubidy MP3 Guide: Music Search & Download Insights
Possible Origins and Interpretations of 9253612736
The origin of a number like 9253612736 can vary widely depending on the system generating it. One of the most common sources is automated database indexing, where systems assign unique identifiers to each new entry. This ensures that every record remains distinct and traceable.
Another possible interpretation is that it originates from telecommunications infrastructure. Mobile networks often assign temporary or permanent identifiers to calls, messages, or devices. These identifiers are essential for routing communication across towers and servers without confusion or overlap.
In financial or transactional environments, similar numeric strings are used as reference IDs. They help track payments, verify transfers, and maintain audit trails. Even if 9253612736 is not directly visible to end users, it may still exist in backend logs that ensure system integrity.
Machine learning systems and analytics platforms also generate such numbers when processing large datasets. Each user session or event can be assigned a unique identifier, allowing systems to analyze behavior patterns without exposing personal information.
While the exact origin of 9253612736 cannot be determined without context, its structure strongly suggests it belongs to one of these automated generation systems. The key takeaway is that such numbers are not random in function—they are carefully designed components of digital architecture.
Role of Numeric Identifiers in Communication Systems
Numeric identifiers like 9253612736 play a critical role in modern communication networks. Every time a call is made, a message is sent, or data is transferred, backend systems rely on structured identifiers to ensure smooth delivery.
In telecommunications, these numbers help route signals between devices and towers. Instead of relying on names or human-readable labels, systems use numeric codes for speed and accuracy. This reduces errors and allows millions of simultaneous connections to function efficiently.
Similarly, internet-based communication platforms assign unique session IDs to track user activity. These identifiers ensure that messages, calls, and data packets reach the correct destination. Without such systems, digital communication would be chaotic and unreliable.
Another important function is load balancing. Numeric identifiers help distribute traffic across servers, preventing overload and maintaining performance stability. For example, when millions of users access a service simultaneously, identifiers ensure requests are handled in an organized manner.
In this context, 9253612736 can be understood as part of a broader ecosystem of structured communication management. It represents how digital systems prioritize efficiency, scalability, and precision in handling global data flows.
9253612736 in Data Tracking and Verification Systems
In modern digital infrastructure, 9253612736 may function as a tracking or verification identifier within complex systems. These identifiers are essential for maintaining data integrity and ensuring that every action within a system is recorded accurately.
Verification systems often use long numeric codes to confirm user identity or transaction authenticity. When a user logs into a platform, makes a payment, or verifies an account, a unique identifier is generated to validate the process. This ensures that unauthorized actions are detected and prevented.
Data tracking systems also rely heavily on such numbers. Every interaction—whether a click, login, or transaction—can be assigned a unique ID. This helps organizations analyze user behavior, improve services, and detect anomalies.
For example, e-commerce platforms use identifiers similar to 9253612736 to track orders from placement to delivery. Each stage of the process is logged using unique numeric codes, ensuring transparency and accountability.
In cybersecurity, these identifiers help detect suspicious activity. If a system notices unusual behavior linked to a specific ID, it can trigger alerts or security protocols.
Thus, 9253612736 symbolizes the backbone of modern digital verification systems, where accuracy and traceability are essential for trust and security.
Security Concerns and Privacy Implications of 9253612736
While numeric identifiers like 9253612736 are essential for system functionality, they also raise important security and privacy considerations. Since these numbers are often linked to user activity or system events, they must be handled with strict confidentiality.
One major concern is data exposure. If identifiers are improperly stored or transmitted, they could potentially be exploited by malicious actors to trace user behavior or system patterns. Although these numbers alone may not reveal personal identity, they can become sensitive when combined with other datasets.
Another issue is unauthorized tracking. In some cases, identifiers can be used to monitor user activity across platforms without consent. This raises ethical questions about transparency and data usage policies.
To mitigate these risks, organizations implement encryption, anonymization, and access controls. These security measures ensure that identifiers like 9253612736 cannot be misused or linked directly to individuals.
Users also play a role in protecting their privacy by being cautious about sharing sensitive information and using secure platforms. Awareness of how such identifiers work helps individuals better understand digital privacy risks.
Ultimately, while 9253612736 serves an important technical function, it also highlights the need for responsible data management and strong cybersecurity practices.
Real-World Applications of Codes Like 9253612736
Numeric identifiers such as 9253612736 are widely used across industries, even if users rarely notice them. In healthcare systems, they are used to track patient records while maintaining confidentiality. Each patient may be assigned a unique ID to ensure accurate medical history management.
In logistics and transportation, similar codes help track shipments across global supply chains. From warehouse to delivery, every package is assigned an identifier that ensures it reaches the correct destination.
Financial institutions rely heavily on numeric identifiers for transaction tracking. Every bank transfer, card payment, or digital wallet transaction generates a unique reference number for auditing and verification purposes.
Technology companies use these identifiers in cloud computing environments. They help manage user sessions, API requests, and system logs efficiently. Without them, large-scale digital services would struggle to maintain order and reliability.
Even social media platforms use internal identifiers to track posts, comments, and user interactions. These systems ensure smooth operation while maintaining data structure behind the scenes.
In all these applications, 9253612736 represents the hidden backbone of digital organization, ensuring systems remain efficient, traceable, and scalable.
Misuse, Spam Risks, and How to Stay Safe
Although numeric identifiers like 9253612736 are generally harmless, they can sometimes appear in spam messages, phishing attempts, or suspicious communications. Cybercriminals may use random numbers to impersonate system-generated alerts or fake verification messages.
Users should be cautious when receiving unexpected messages containing unknown numeric codes. If a number appears in a message asking for personal information or urgent action, it should be treated with skepticism.
One common tactic used in scams is pretending that a numeric identifier is linked to account security or financial activity. These messages often attempt to trick users into revealing sensitive data.
To stay safe, users should verify the source of any message containing such identifiers. Official organizations rarely ask for sensitive information through random numbers or unsolicited communication.
It is also advisable to use spam filters, enable two-factor authentication, and regularly monitor account activity. These practices help reduce the risk of falling victim to scams involving numeric identifiers.
While 9253612736 itself is not inherently dangerous, awareness and caution are essential in today’s digital environment where such numbers can be misused.
Conclusion
The exploration of 9253612736 highlights the broader role of numeric identifiers in modern digital systems. While it may appear as a simple number, it represents the complex infrastructure that powers communication, verification, and data management across industries.
From telecommunications to cybersecurity, such identifiers ensure accuracy, efficiency, and scalability. They enable systems to handle vast amounts of data while maintaining order and traceability.
At the same time, understanding these numbers helps users become more aware of privacy and security considerations in the digital age. Whether used in tracking, authentication, or analytics, identifiers like 9253612736 are essential components of today’s technological ecosystem.
Ultimately, recognizing their purpose allows us to better appreciate the invisible systems that keep our digital world running smoothly.
Read More: Legendbio.co.uk
Tech
How Usability Testing for Mobile Apps Improves Retention and Engagement
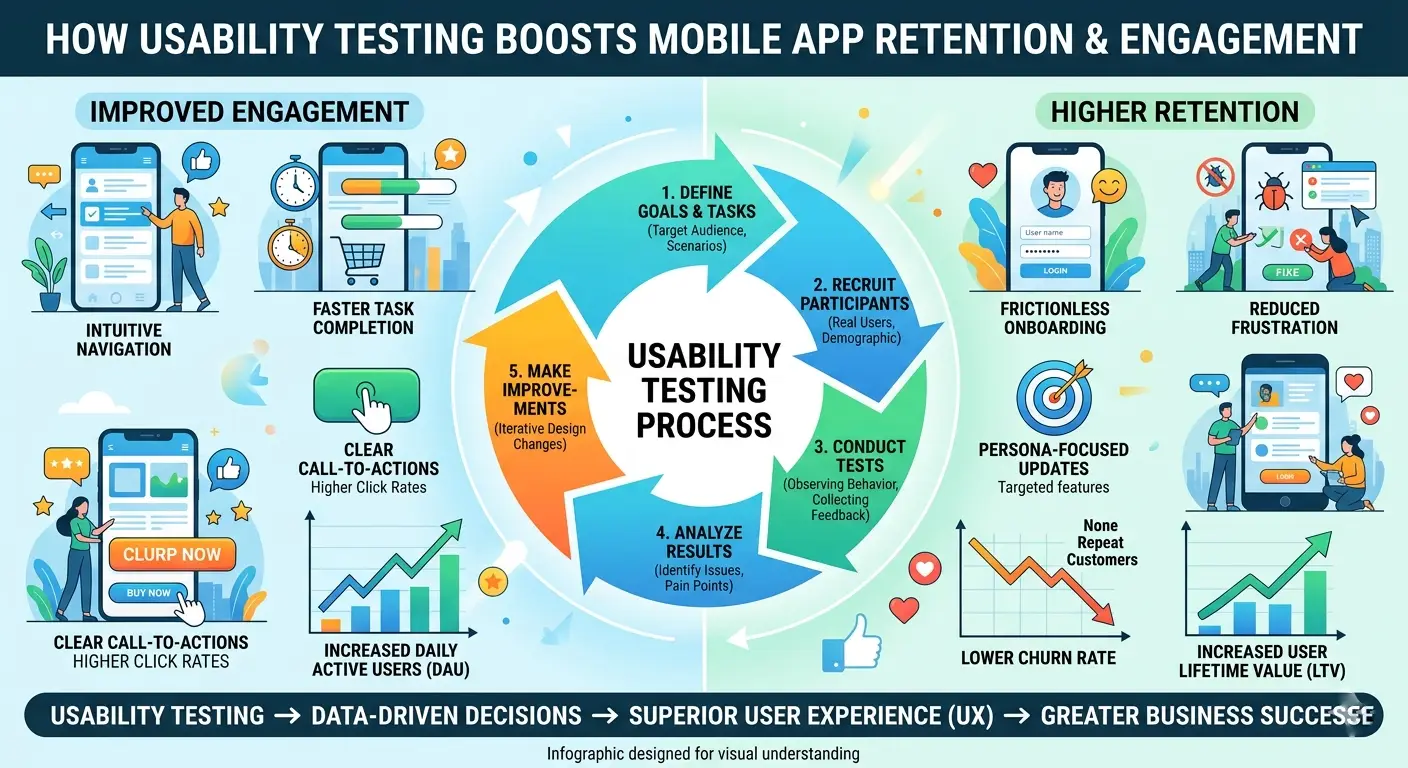
Marketing can bring users to a mobile app, but the experience is what makes them stay. People judge an app very quickly. If it feels confusing, slow, or difficult to navigate, they are likely to leave. Usability Testing for Mobile Apps helps teams understand these moments by showing how users move through the app, where friction appears, and what affects retention.
Features can attract attention, but they do not guarantee retention. What keeps users coming back is an experience that feels simple, fast, and reliable. When tasks are easy to complete, people stay engaged, use more of the product, and return more naturally. Usability Testing in customer retention helps uncover the points where users struggle, so teams can fix them before those issues lead to churn.
A well-tested app does more than function correctly. It feels intuitive. That difference directly affects session length, repeat usage, reviews, referrals, and long-term value.
Why Usability Testing for Mobile Apps Matters for User Retention
Early user experience has a direct impact on retention. Users want a product that feels easy from the start. If onboarding is confusing, menus feel packed, or the main actions are not easy to find, the app can lose momentum before users feel comfortable enough to continue.
Here is what users expect from a strong mobile experience:
- Clear navigation from the first screen
- Fast task completion without second-guessing
- Familiar patterns that reduce effort
- Readable content and obvious next steps
- Smooth interactions across devices and screen sizes
- Confidence that their time is not being wasted
When these expectations are met, engagement improves naturally. Users do not need to think about how the app works. They focus on what they came to do.
A key benefit of Usability Testing is that it brings real user behavior into focus. Rather than depending on internal assumptions, teams can see where people hesitate, get confused, or lose momentum. Even minor design issues like vague labels or missed buttons can quietly weaken retention.
Usability Testing for Mobile Apps Helps Identify Drop-Off Triggers
A user rarely leaves an app for one dramatic reason. Most churn comes from a series of small frustrations that build up. Usability Testing for mobile apps helps uncover these moments early, especially when analytics alone only show what happened, not why it happened.
Common retention killers include:
- Overcomplicated sign-up flows
- Too many steps to complete a simple action
- Weak search or filtering experience
- Inconsistent gestures or navigation patterns
- Poor readability on smaller screens
- Slow or unclear feedback after taps and actions
- Checkout or conversion journeys with hidden friction
These are not just interface problems. They are business problems. If users cannot move smoothly through key journeys, they engage less, convert less, and return less.
Teams that invest in structured observation often discover that what seemed minor internally feels major to users. This is why many growth-focused brands use usability testing services to validate real-world behavior before scaling product decisions.
How Usability Testing for Mobile Apps Improves Engagement
Engagement grows when users feel satisfied, in control, and confident. That confidence comes from interaction quality. When users know what to do next and feel successful doing it, they stay longer and return more often. It helps teams create that kind of rhythm.
It improves engagement by showing how users respond to:
- Onboarding flow and first-use experience
- Content hierarchy and visual clarity
- Placement of actions, prompts, and CTAs
- Personalization flows and settings
- Notifications and re-engagement prompts
- Search, browse, and discovery behavior
- Error states and recovery experiences
Better engagement does not always require adding more features. Sometimes it comes from removing confusion. A shorter flow, clearer icon, or better content label can have a measurable impact on repeat use.
This is also where Usability Testing to optimize your app makes a real difference. It helps teams fix the moments that shape everyday use, beyond visual design alone.
How to Perform Mobile App Usability Testing Effectively
Knowing How to perform mobile app usability testing matters if you want useful insights instead of general comments. The aim is to watch how people actually use the app, not just ask what they think. When real users complete real tasks, teams can clearly see what slows them down.
A simple and effective process looks like this:
- Define the objective clearly
- Are you improving onboarding, checkout, discovery, or retention?
- Recruit participants that match your actual user profile
- Test with relevant users, not just internal teams
- Create task-based scenarios
- Ask users to complete realistic actions inside the app
- Observe without over-explaining
- Let behavior reveal confusion points naturally
- Track both completion and hesitation
- Success rates matter, but pauses and uncertainty matter too
- Capture qualitative and quantitative patterns
- Combine user comments with time, clicks, and errors
- Prioritize fixes by user impact
- Solve what affects key journeys first
The strongest studies are focused and repeatable. A few honest test sessions can reveal more than weeks of internal debate.
What Teams Gain Beyond Better UX
Usability testing does not only benefit design teams. Its impact is very wide, especially for businesses trying to improve retention and product performance.
Cross-functional gains often include:
- Product teams get better clarity on feature priorities
- Marketing teams understand where user expectations break
- Support teams see recurring pain points before tickets rise
- Leadership gets evidence for decision-making
- Designers create with more confidence and less guesswork
In many cases, testing makes UX Design services more effective by connecting design decisions to real user behavior instead of personal opinion. It also helps guide better choices in Mobile app development, where each release should make the app easier to use, not just more feature-rich.
Why Mobile App Usability Shapes Long-Term Retention
An app succeeds when it feels simple, clear, and easy to return to. People stay engaged when they can find what they need, trust the experience, and complete tasks without effort. That is why testing is important. It helps teams spot the parts that feel difficult before those issues affect retention.
Focus on what users need:
- Less effort
- More clarity
- Faster completion
- Better flow
- Greater confidence
When an app sees early drop-offs, low engagement, or weak repeat usage, the issue is often not visibility but usability. Watching how users move through the app helps teams understand what needs to be made simpler, clearer, or easier to use. That is where retention begins, which is why this approach continues to be one of the most effective ways to build better digital products.
Tech
vRealize Infrastructure Navigator Guide: VMware Visibility Mastery
Modern virtualized environments demand deep visibility into application dependencies and infrastructure relationships, especially in large-scale VMware ecosystems. One of the tools designed to address this challenge is vRealize Infrastructure Navigator, which provides application-aware discovery and mapping across virtual machines. It helps administrators understand how applications interact within a complex infrastructure, reducing downtime risks and improving troubleshooting efficiency. In environments where services are highly interconnected, having a clear dependency map is no longer optional but essential. This makes VMware’s ecosystem management significantly more intelligent and proactive when properly utilized.
In this guide, we will explore how vRealize Infrastructure Navigator functions, its architecture, deployment strategies, and real-world applications. We will also examine its integration with VMware platforms and its relevance in modern cloud infrastructures. As virtualization continues to evolve, understanding tools like this becomes critical for IT professionals managing enterprise workloads at scale.
Understanding vRealize Infrastructure Navigator Architecture
The architecture of this tool is built to seamlessly integrate with VMware vCenter, enabling automatic discovery of application relationships without requiring agents inside guest operating systems. It uses a combination of hypervisor-level introspection and network traffic analysis to map dependencies between virtual machines and services. This non-intrusive approach allows it to operate with minimal performance overhead while still delivering accurate insights into application topology.
At its core, vRealize Infrastructure Navigator relies on a virtual appliance that communicates directly with vCenter Server. It collects metadata about running applications and builds a dynamic map of interactions between services. This architecture ensures that even complex multi-tier applications are visualized clearly, helping administrators identify bottlenecks or potential failure points quickly.
Another key component is its dependency mapping engine, which continuously updates relationships as workloads change. This dynamic nature is particularly useful in environments where virtual machines are frequently migrated or scaled. By maintaining real-time awareness, the system ensures that infrastructure visibility remains accurate and actionable.
Additionally, it supports integration with VMware tools such as vRealize Operations Manager, enhancing monitoring capabilities by adding contextual application intelligence. This layered architecture transforms raw infrastructure data into meaningful operational insights, enabling better decision-making across IT environments.
Will You Check This Article: Theliorstore.me: Digital Shopping Evolution Guide
Core Features and Dependency Mapping Capabilities
One of the most powerful aspects of vRealize Infrastructure Navigator is its ability to automatically discover application dependencies without manual configuration. This feature eliminates the need for time-consuming documentation of service relationships, which is often outdated in dynamic environments. Instead, it continuously analyzes system behavior to build accurate dependency maps.
The tool provides visual topology maps that represent how applications communicate across virtual machines. These maps allow administrators to identify critical dependencies, such as database connections, middleware interactions, and front-end service links. By visualizing these relationships, IT teams can better understand the impact of system changes or failures.
Another important capability is change tracking. Whenever a virtual machine is modified, moved, or restarted, the system updates its dependency data accordingly. This ensures that infrastructure visibility remains current even in highly dynamic cloud environments. It also helps reduce downtime by enabling faster root cause analysis during incidents.
The platform also enhances operational efficiency by supporting application grouping. Related services can be categorized into logical application stacks, making it easier to manage large-scale deployments. This is particularly useful for enterprises running hundreds or thousands of virtual machines across multiple clusters.
Overall, these features make the tool a valuable asset for organizations seeking improved visibility and control over their virtualized infrastructure.
vRealize Infrastructure Navigator Deployment in VMware Environments
Deploying vRealize Infrastructure Navigator requires careful planning to ensure optimal integration with existing VMware infrastructure. The deployment typically begins with importing the virtual appliance into a vSphere environment, followed by configuration with vCenter Server. Once connected, the system begins scanning virtual machines to identify running applications and their interactions.
Proper network configuration is essential for successful deployment. The appliance must have access to all relevant ESXi hosts and virtual machines to accurately collect dependency data. In larger environments, administrators often deploy multiple instances to ensure scalability and performance efficiency.
Security considerations also play a crucial role during deployment. Since the tool interacts closely with vCenter, it requires appropriate permissions and role-based access control settings. Ensuring secure communication between components helps maintain the integrity of collected data.
After deployment, initial discovery may take some time depending on the size of the environment. Once complete, administrators gain access to a fully mapped application topology. This visibility significantly improves operational awareness and simplifies infrastructure management tasks.
Integration with vCenter and vRealize Suite
A major strength of this tool lies in its tight integration with VMware vCenter, which serves as the central management platform for virtual environments. Through this integration, it can access real-time information about virtual machines, hosts, and clusters without requiring additional agents.
When combined with the broader vRealize Suite, its capabilities expand significantly. For example, integration with vRealize Operations Manager allows for enhanced performance monitoring using application-aware metrics. This means administrators can correlate infrastructure health with application behavior, leading to more accurate diagnostics.
Additionally, integration enables automated workflows that respond to changes in dependency structures. For instance, if a critical application component fails, alerts can be triggered within the vRealize ecosystem to initiate remediation processes. This level of automation improves system resilience and reduces manual intervention.
The seamless interoperability between these tools creates a unified management experience. It bridges the gap between infrastructure monitoring and application awareness, allowing IT teams to operate with greater efficiency and precision.
Performance Monitoring and Application Awareness
Performance monitoring becomes significantly more effective when combined with application-level awareness. vRealize Infrastructure Navigator enhances traditional monitoring tools by adding context to performance data. Instead of viewing metrics in isolation, administrators can understand how application dependencies influence system behavior.
For example, if a virtual machine experiences high CPU usage, the tool can help identify which connected services are contributing to the load. This allows for faster root cause identification and more targeted troubleshooting. It also helps prevent unnecessary resource scaling by pinpointing actual performance bottlenecks.
Application awareness also improves capacity planning. By understanding how services interact, organizations can better predict infrastructure requirements and optimize resource allocation. This leads to more efficient use of compute, storage, and network resources.
Furthermore, historical dependency data can be used to analyze performance trends over time. This is particularly useful in identifying recurring issues or inefficiencies within application architectures. Overall, this level of insight transforms monitoring from reactive to proactive management.
Use Cases in Enterprise Virtualization Management
In enterprise environments, vRealize Infrastructure Navigator is widely used for application dependency mapping during data center modernization projects. When organizations migrate workloads to virtualized or hybrid cloud environments, understanding application relationships is critical to ensuring smooth transitions.
Another common use case is disaster recovery planning. By visualizing application dependencies, IT teams can identify which systems are critical for business continuity. This allows for more effective recovery strategies and reduces downtime during unexpected failures.
The tool is also valuable during infrastructure audits and compliance assessments. It provides detailed documentation of application interactions, which can be used to meet regulatory requirements or internal governance standards. This reduces the manual effort required for documentation and improves accuracy.
Additionally, it supports optimization initiatives by identifying underutilized or redundant services. This helps organizations streamline their infrastructure and reduce operational costs while maintaining performance and reliability.
Challenges, Limitations, and Modern Alternatives
Despite its advantages, vRealize Infrastructure Navigator also has certain limitations that organizations must consider. One of the primary challenges is its dependency on VMware environments, which limits its applicability in multi-cloud or heterogeneous infrastructures. As modern IT environments become increasingly diverse, this can be a significant constraint.
Another limitation is that the product has been deprecated in favor of more advanced solutions within the VMware ecosystem. This means organizations may need to transition to newer tools for long-term support and enhanced functionality. Migration planning becomes essential in such scenarios.
Additionally, while the tool provides strong dependency mapping, it may not always capture every dynamic interaction in highly complex microservices architectures. This can result in partial visibility in certain modern application environments.
Modern alternatives, such as advanced observability platforms and cloud-native monitoring tools, offer broader compatibility and deeper analytics capabilities. These solutions often integrate AI-driven insights and multi-cloud support, making them more suitable for evolving IT landscapes.
Conclusion
vRealize Infrastructure Navigator has played a significant role in transforming how organizations visualize and manage application dependencies within VMware environments. Its ability to provide automated discovery, real-time mapping, and deep infrastructure insight has made it a valuable tool for virtualization management. Although newer solutions have emerged, its foundational concepts continue to influence modern observability and infrastructure intelligence platforms.
As enterprises move toward hybrid and cloud-native architectures, understanding tools like vRealize Infrastructure Navigator remains important for grasping the evolution of infrastructure visibility. It highlights the growing need for application-aware monitoring and intelligent dependency management in today’s complex digital ecosystems.
Read More: Legendbio.co.uk
Tech
Theliorstore.me: Digital Shopping Evolution Guide

In today’s rapidly evolving digital economy, online shopping platforms are reshaping how consumers discover, evaluate, and purchase products. Among these emerging digital spaces, theliorstore.me stands out as a concept that reflects the shift toward streamlined e-commerce ecosystems designed for convenience, accessibility, and user-focused experiences. It represents more than just an online storefront; it symbolizes how modern digital marketplaces integrate design, functionality, and customer engagement into one unified structure. As consumers increasingly rely on online platforms for everyday needs, understanding such ecosystems becomes essential for both shoppers and digital entrepreneurs.
The rise of platforms like theliorstore.me highlights the growing importance of digital transformation in retail. From intuitive navigation to secure transactions and optimized product visibility, every element plays a role in shaping customer trust and satisfaction. This article explores the structure, usability, and strategic potential behind such platforms, offering a deep dive into how they function and why they matter in today’s competitive online marketplace landscape.
Theliorstore.me Digital Marketplace Architecture
The foundation of any successful e-commerce platform lies in its architecture, and theliorstore.me reflects a modern approach to building scalable and user-friendly digital storefronts. Its structure is typically designed around clean navigation layers, responsive layouts, and optimized backend systems that support seamless browsing experiences. This ensures that users can quickly locate products without unnecessary complexity or confusion.
Another key aspect of theliorstore.me architecture is its adaptability to multiple devices. Whether accessed through mobile, tablet, or desktop, the platform is designed to maintain consistent performance and visual integrity. This responsiveness is essential in today’s mobile-first environment, where a majority of users shop directly from smartphones. Efficient load times, categorized menus, and search optimization further enhance usability.
Additionally, backend integration plays a critical role in managing inventory, updating product listings, and ensuring smooth transactions. The architecture of theliorstore.me demonstrates how modern e-commerce platforms combine frontend aesthetics with robust technical infrastructure to create a balanced digital ecosystem.
Will You Check This Article: Sourthrout Relief Guide: Causes, Symptoms & Healing Tips
User Experience and Interface Navigation
User experience is a defining factor in determining the success of any online platform, and theliorstore.me places strong emphasis on intuitive interaction design. The interface is typically structured to reduce friction, allowing users to move seamlessly from browsing to checkout without unnecessary steps. Clear typography, visually appealing layouts, and strategically placed call-to-action buttons contribute to an efficient shopping journey.
Navigation systems within the platform are designed to prioritize simplicity. Categories are logically organized, enabling users to filter products based on relevance, popularity, or price. This structured approach reduces cognitive load and improves decision-making efficiency. In addition, search functionality is often enhanced with predictive text and smart filtering systems.
Another important aspect of user experience is accessibility. Platforms like theliorstore.me aim to ensure inclusivity by maintaining readability standards, color contrast optimization, and mobile responsiveness. These design choices collectively contribute to a smoother, more engaging user journey that encourages repeat visits and long-term engagement.
Product Organization and Digital Catalog Strategy
A well-structured product catalog is essential for any e-commerce platform, and systems like theliorstore.me rely heavily on organized categorization to improve discoverability. Products are typically grouped into relevant categories and subcategories, allowing users to quickly locate items that match their intent. This structured approach enhances both user satisfaction and conversion rates.
High-quality product presentation is another cornerstone of effective catalog management. Detailed descriptions, clear imagery, and specification breakdowns help users make informed purchasing decisions. In digital environments where physical inspection is not possible, this transparency becomes even more critical.
Furthermore, dynamic inventory updates ensure that product availability remains accurate. Real-time synchronization between backend databases and frontend displays prevents user frustration caused by outdated listings. Together, these elements make theliorstore.me-style platforms efficient digital marketplaces that prioritize clarity, organization, and reliability in product presentation.
Security Framework and Payment Reliability
Security is one of the most important pillars of any online shopping ecosystem, and platforms like theliorstore.me are expected to implement strong protective measures. Encryption protocols such as SSL ensure that user data remains secure during transactions, reducing the risk of unauthorized access or data breaches. This builds essential trust between the platform and its users.
Payment systems are typically integrated with reliable gateways that support multiple methods, including credit cards, digital wallets, and bank transfers. These systems are designed to process transactions quickly while maintaining strict verification procedures. Fraud detection mechanisms also play a vital role in monitoring suspicious activities and preventing financial misuse.
In addition to payment security, user privacy policies ensure that personal information is handled responsibly. Transparent data practices help reinforce consumer confidence. Altogether, these security frameworks contribute to making platforms like theliorstore.me dependable environments for digital commerce.
SEO Optimization and Digital Visibility Strategy
For any online marketplace, visibility is crucial, and SEO plays a major role in driving organic traffic. Platforms similar to theliorstore.me often rely on keyword optimization, metadata structuring, and content hierarchy to improve search engine rankings. This ensures that potential customers can easily discover the platform through search engines.
Content strategy is another important element. Product descriptions, category pages, and blog content are often optimized to include relevant keywords and semantic variations. This helps search engines understand the platform’s relevance to user queries while maintaining readability for human visitors.
Backlinking strategies and domain authority building further enhance visibility. When reputable websites reference or link to a platform, its credibility increases in the eyes of search engines. Together, these SEO techniques help strengthen the online presence of theliorstore.me-style platforms in competitive digital markets.
Customer Support Systems and Engagement Models
Customer support is a critical component of user satisfaction in any digital marketplace. Platforms like theliorstore.me typically incorporate multiple support channels such as live chat, email assistance, and help centers. These systems ensure that users can quickly resolve issues related to orders, payments, or product inquiries.
Engagement strategies also extend beyond support. Personalized recommendations, email notifications, and loyalty programs are commonly used to maintain user interest. These features help create a more interactive and tailored shopping experience that aligns with individual preferences.
Feedback systems further enhance engagement by allowing users to share reviews and ratings. This not only helps future customers make informed decisions but also provides valuable insights for platform improvement. In this way, customer engagement becomes a continuous cycle of interaction and refinement.
Theliorstore.me and Future Growth in E-Commerce
The future of theliorstore.me and similar platforms is closely tied to advancements in digital commerce technology. As artificial intelligence, automation, and machine learning continue to evolve, these systems are expected to become more personalized and predictive in nature. This will allow platforms to anticipate user needs and offer tailored shopping experiences.
Scalability is another important factor influencing future growth. As user demand increases, platforms must be capable of handling higher traffic volumes without compromising performance. Cloud-based infrastructure and distributed systems play a key role in supporting this expansion.
Additionally, integration with emerging technologies such as augmented reality and voice commerce may redefine how users interact with digital marketplaces. These innovations have the potential to transform theliorstore.me into a more immersive and intelligent shopping ecosystem.
Conclusion
theliorstore.me represents a broader shift in how digital marketplaces are structured, optimized, and experienced by users. It reflects the convergence of technology, design, and consumer behavior into a unified online shopping environment that prioritizes efficiency and engagement. From architecture to security and SEO strategy, every element contributes to building a seamless digital commerce experience.
As e-commerce continues to evolve, platforms like theliorstore.me will play an increasingly important role in shaping consumer expectations and industry standards. Their success will depend on adaptability, innovation, and user-centric design principles. Ultimately, theliorstore.me stands as a symbol of the modern digital retail landscape, where convenience, trust, and technology intersect to define the future of online shopping.
Read More: Legendbio.co.uk
-

 Business1 week ago
Business1 week agoSongoftruth.org Guide: Meaning, Purpose and Online Presence
-

 Tech1 week ago
Tech1 week agoWhere is Area Code 682 Located? Full Texas Guide & Details
-

 Tech1 week ago
Tech1 week agoDevCheck Guide: Master Your Device Diagnostics Easily
-

 Business1 week ago
Business1 week agoBoelis Guide: Complete Deep Dive into Modern Boelis System
-

 Entertainment1 week ago
Entertainment1 week agoTubidy MP3 Guide: Music Search & Download Insights
-
 Celebrity5 days ago
Celebrity5 days agoSandra Janowski: Life, Legacy, and Public Curiosity Explored
-

 Celebrity7 days ago
Celebrity7 days agoJack Şoparov: Vision, Strategy & Digital Influence Era
-

 Business1 week ago
Business1 week agoWRE Inc Explained: Growth, Services, Strategy & Market Role Today




