Tech
Where is Area Code 682 Located? Full Texas Guide & Details

Area codes often tell us more than just numbers; they reveal regions, calling patterns, and even population growth. One such area code that people frequently search for is where is area code 682 located, especially when they receive unexpected calls from it. Many people get curious or even confused when they see this number pop up on their phone. Understanding it can help you identify callers and know the region better. In this guide, we will break it down in a very simple and clear way. You will learn what state it belongs to, which cities use it, and why it exists in the first place. Let’s explore everything step by step.
Area Code 682 and where is area code 682 located Explained
When people ask where is area code 682 located, the simple answer is that it is in the United States, specifically in Texas. This area code is not tied to just one small town but covers a large and busy region. It is mainly used in the northern part of Texas, especially around the Dallas–Fort Worth metro area. This region is one of the fastest growing urban zones in the country.
The demand for phone numbers in this area became so high that a new area code had to be introduced. That is how 682 came into existence. It works alongside other area codes in the same region. So, when you see this number, it is connected to a major Texas metropolitan area with millions of residents and businesses.
Will You Check This Article: Songoftruth.org Guide: Meaning, Purpose and Online Presence
Geographic Coverage of Area Code 682 Region
The question where is area code 682 located becomes clearer when we look at its geographic spread. It mainly serves the Fort Worth side and surrounding counties in North Texas. This includes both urban cities and suburban communities.
The area is part of the larger Dallas–Fort Worth metroplex, which is one of the biggest economic zones in the United States. It includes a mix of residential neighborhoods, corporate offices, schools, and industries. Because of this wide usage, the area code is not limited to a single city but shared across many locations.
Origin and History Behind Area Code 682 System
To understand where is area code 682 located, we should also know how it started. This area code was introduced as an overlay due to the increasing population in North Texas. Before it existed, area codes like 817 were heavily used and started running out of available numbers.
Instead of splitting regions into smaller zones, authorities introduced 682 as an overlay. This means both old and new area codes work in the same geographic area. This system helps avoid changing existing numbers while still providing new ones for growing demand.
Major Cities Covered Under Area Code 682
When looking at where is area code 682 located, it is important to know the major cities it includes. Fort Worth is the primary city associated with this code. However, it also covers surrounding areas such as Arlington, Irving, and parts of Denton County.
These cities are important hubs for business, education, and transportation. Many companies and service providers use this area code. Because of this, residents may see calls from 682 numbers frequently in their daily lives.
Overlay System and Connection with Other Codes
Another key detail in understanding where is area code 682 located is its relationship with other area codes. It works as an overlay with area codes like 817 and 214 in certain parts of North Texas.
This means multiple area codes exist in the same geographic region. People living in the same neighborhood might have different area codes even though they are in the same city. This system is designed to handle the growing number of mobile phones and landlines.
Calling Patterns and Dialing Rules in This Area
When discussing where is area code 682 located, it is also useful to understand how calling works there. Because it is an overlay region, 10-digit dialing is required. This means you must dial the area code even for local calls.
This rule helps the phone system distinguish between different numbers in the same area. It may feel different for people used to older dialing systems, but it is now standard in this region. Most residents are already familiar with it.
Common Misunderstandings and Spam Call Concerns
Many people searching where is area code 682 located are actually trying to identify unknown calls. Sometimes, numbers from this area code may appear as spam or telemarketing calls.
However, it is important to understand that not all calls from this area code are suspicious. It is widely used by real businesses, government offices, and individuals. Still, like any busy area code, it can sometimes be used for unwanted calls, so caution is always helpful.
Conclusion
In conclusion, where is area code 682 located is a question linked directly to North Texas in the United States, mainly around the Fort Worth and Dallas–Fort Worth metro area. It is part of an overlay system created to support the growing population and increasing demand for phone numbers. This area code shares its region with others like 817 and serves a wide mix of cities, businesses, and communities.
Understanding where is area code 682 located helps you recognize calls, avoid confusion, and better understand how the U.S. phone system is organized. It is not a random or foreign code but a key part of a large and active region in Texas.
Read More: Legendbio.co.uk
Tech
EmailSecureserver: Advanced Email Security Guide for Modern Protection

In today’s hyper-connected digital ecosystem, email remains one of the most critical communication channels for businesses and individuals alike. However, with its importance comes vulnerability, as cybercriminals continuously exploit weak systems to steal data, inject malware, and launch phishing campaigns. This is where emailsecureserver technology becomes essential, offering a fortified environment designed to protect sensitive communication. As organizations scale globally, the need for advanced protection is no longer optional but a foundational requirement.
The evolution of email security has shifted from simple spam filters to intelligent, multi-layered defense systems capable of detecting threats in real time. Modern infrastructures now integrate encryption, authentication protocols, and AI-driven monitoring to safeguard every message. Within this landscape, emailsecureserver solutions stand out as a powerful framework ensuring data integrity and secure transmission. Understanding how these systems operate can help businesses reduce risk and improve trust.
This guide explores the architecture, features, and real-world applications of secure email systems in depth. You will learn how modern protection works, why it is essential, and how organizations can maximize its effectiveness.
What is EmailSecureserver and Why It Matters
The concept of emailsecureserver refers to a dedicated email hosting and protection system designed to secure incoming and outgoing messages through layered cybersecurity mechanisms. Unlike traditional email systems that rely on basic spam filtering, this advanced framework focuses on encryption, threat detection, and secure routing to ensure data remains protected at all times. It acts as both a gateway and a shield, filtering harmful content before it reaches the user.
In modern digital environments, email is often the primary entry point for cyberattacks. Hackers use phishing links, spoofed domains, and malicious attachments to exploit vulnerabilities. A properly configured emailsecureserver helps eliminate these risks by scanning every packet of data in real time. This ensures that sensitive business communication is not exposed to unauthorized access or interception.
Another critical aspect of its importance lies in regulatory compliance. Many industries, such as finance and healthcare, require strict data protection standards. Implementing a secure email infrastructure helps organizations meet compliance requirements while maintaining operational efficiency. Ultimately, emailsecureserver systems are not just technical tools—they are essential security frameworks for digital survival.
Will You Check This Article: Educationbeing.com: Modern Learning & Growth Hub Guide
Core Architecture of Secure Email Systems
The architecture behind a secure email system is built on multiple interconnected layers that work together to ensure safe communication. At the foundation lies the mail transfer agent (MTA), responsible for routing emails between servers. In a emailsecureserver environment, this layer is enhanced with security filters that inspect metadata and sender authenticity before allowing transmission.
Above this layer sits the content filtering system, which analyzes email body content, attachments, and embedded links. This system uses pattern recognition and machine learning to detect suspicious behavior. Additionally, sandboxing technology isolates unknown attachments in a controlled environment to prevent malware execution.
The final layer involves authentication protocols such as SPF, DKIM, and DMARC. These ensure that emails are genuinely sent from verified domains and have not been tampered with during transit. A fully optimized emailsecureserver integrates all these layers seamlessly, creating a unified defense structure that reduces vulnerabilities while maintaining performance efficiency.
Key Features That Strengthen EmailSecureserver Platforms
Modern emailsecureserver platforms are equipped with advanced features designed to combat evolving cyber threats. One of the most important features is real-time threat intelligence integration. This allows the system to continuously update its database with known malicious sources, ensuring proactive defense against new attacks.
Another essential feature is multi-layer spam filtering. Instead of relying on a single filter, these systems use multiple detection engines to analyze email patterns, sender reputation, and behavioral anomalies. This significantly reduces false positives while improving detection accuracy.
Data loss prevention (DLP) is also a core feature, ensuring that sensitive information such as passwords, financial data, or personal identifiers does not leave the organization without authorization. Combined with encryption and secure storage, emailsecureserver platforms provide a robust ecosystem that enhances both security and productivity in professional communication environments.
Encryption Standards and Data Protection Mechanisms
Encryption plays a central role in the effectiveness of any secure email system. In a emailsecureserver setup, encryption ensures that data remains unreadable during transmission and storage unless accessed by authorized recipients. The most commonly used standards include TLS (Transport Layer Security) and end-to-end encryption protocols.
TLS encryption secures the communication channel between email servers, preventing interception during transit. Meanwhile, end-to-end encryption ensures that only the sender and recipient can decode the message content, eliminating the risk of server-side exposure. This dual-layer encryption approach significantly strengthens communication security.
In addition to encryption, modern systems also use hashing algorithms and digital signatures to verify message integrity. These mechanisms ensure that emails are not altered during transmission. By combining these techniques, emailsecureserver infrastructures provide a highly secure environment where confidentiality and authenticity are maintained at all times.
Threat Landscape: Spam, Phishing, and Malware Defense
Cyber threats targeting email systems continue to evolve in complexity and scale. Spam emails are no longer just annoying advertisements; they often serve as carriers for malicious payloads. A strong emailsecureserver is designed to identify and block these threats before they reach the inbox.
Phishing attacks remain one of the most dangerous threats, where attackers impersonate trusted entities to steal sensitive information. Advanced email security systems use domain authentication and behavioral analysis to detect spoofed messages and prevent users from interacting with harmful content.
Malware distribution through email attachments is another major concern. Cybercriminals often disguise harmful files as legitimate documents. To counter this, secure email systems use sandbox environments to execute attachments safely before delivery. This ensures that any malicious activity is detected and neutralized early, reinforcing the protective capabilities of emailsecureserver solutions.
EmailSecureserver Integration with Modern Businesses
Modern enterprises rely heavily on digital communication, making secure email systems a vital part of IT infrastructure. A well-implemented emailsecureserver integrates seamlessly with business applications such as CRM systems, cloud storage platforms, and collaboration tools. This ensures secure data flow across all departments.
One of the biggest advantages of integration is centralized security management. IT administrators can monitor all email activity from a single dashboard, enabling faster threat detection and response. This centralized approach reduces complexity and improves operational efficiency.
Additionally, integration enhances scalability. As businesses grow, their communication needs expand. A flexible emailsecureserver infrastructure can adapt to increased traffic without compromising security. This makes it an ideal solution for startups, SMEs, and large enterprises alike, ensuring consistent protection across all communication channels.
Best Practices for Maximizing Email Security Efficiency
To fully leverage the capabilities of a emailsecureserver, organizations must follow a set of best practices. Regular system updates are essential to ensure that security protocols remain effective against new threats. Cybercriminals constantly evolve their methods, and outdated systems become easy targets.
User awareness training is another critical factor. Employees should be educated about phishing attempts, suspicious attachments, and safe email practices. Even the most advanced system can be compromised by human error, making awareness a key component of email security.
Additionally, organizations should implement multi-factor authentication (MFA) and strong password policies. These measures add extra layers of protection, ensuring that unauthorized access is minimized. When combined with technical safeguards, these practices significantly enhance the effectiveness of emailsecureserver systems.
Conclusion
The future of digital communication depends heavily on the continuous evolution of secure email technologies. As cyber threats become more sophisticated, the role of emailsecureserver systems will become even more critical in safeguarding sensitive information. Emerging technologies such as artificial intelligence, machine learning, and behavioral analytics will further strengthen threat detection and response capabilities.
Organizations that invest in advanced email security today are better positioned to handle future risks. A robust emailsecureserver not only protects communication but also builds trust with clients, partners, and stakeholders. It ensures that data integrity, confidentiality, and compliance are maintained across all channels.
Ultimately, the future will demand smarter, faster, and more adaptive security systems. Businesses that adopt these innovations early will gain a significant advantage in the digital landscape, ensuring resilience in an ever-changing cybersecurity environment.
Read More: Cryptoboostly.co.uk
Tech
Antennino: Next-Gen Smart Antenna Revolution
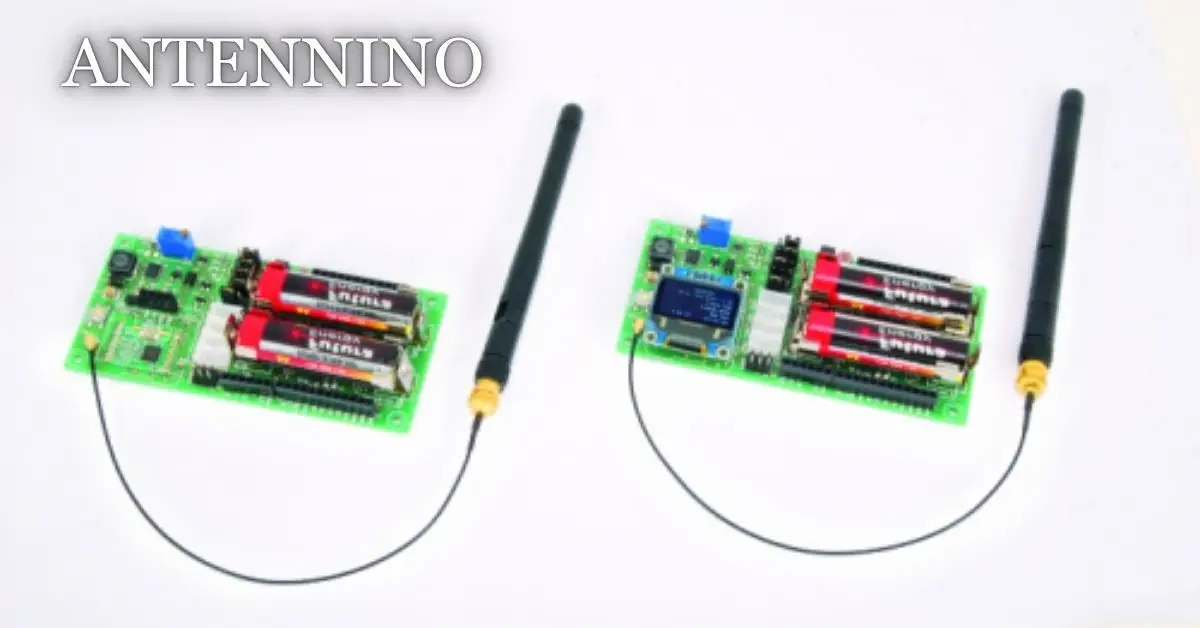
In today’s rapidly evolving digital world, wireless communication has become the backbone of nearly every modern system, from smartphones to smart cities. As connectivity demands grow, traditional antenna technologies struggle to keep up with speed, efficiency, and adaptability requirements. This is where innovation-driven solutions step in to redefine performance standards.
One such emerging concept is antennino, a forward-looking approach that blends intelligent signal processing with advanced antenna engineering. It represents a shift toward smarter, more responsive communication systems capable of handling complex data environments with ease.
The rise of IoT, 5G, and edge computing has further accelerated the need for adaptive wireless frameworks. Antennino-like systems aim to bridge performance gaps and enhance real-time responsiveness in communication networks.
Unlike conventional antennas that operate with fixed parameters, this new paradigm focuses on dynamic optimization and environmental awareness. This makes it highly relevant in modern engineering challenges.
Ultimately, understanding this innovation helps us appreciate the future direction of wireless connectivity and its role in shaping a hyper-connected world.
Understanding Antennino Technology
The concept of antennino revolves around the idea of smart, adaptive antenna systems designed to improve signal transmission efficiency and reliability. Unlike traditional antennas, which rely on static configurations, this system adapts dynamically based on environmental conditions and signal requirements. It is built on the foundation of intelligent feedback mechanisms that continuously refine performance.
At its core, the technology integrates signal optimization algorithms with advanced electromagnetic design principles. This allows it to respond in real time to interference, distance variations, and bandwidth demands. The result is a more stable and efficient communication channel capable of supporting modern data-heavy applications.
Another defining aspect is its ability to reduce signal loss while maximizing coverage. This makes it highly suitable for environments where connectivity is often disrupted, such as dense urban areas or industrial zones. By continuously adjusting its parameters, it ensures consistent communication quality.
In essence, antennino represents a shift from passive reception to active intelligence in antenna systems. It is not just a hardware upgrade but a conceptual evolution in wireless communication design.
Will You Check This Article: Roata Ferris: History, Engineering, and Timeless Appeal
Core Architecture and Signal Processing
The architecture behind advanced antennino systems is built on a combination of hardware precision and software intelligence. It typically includes multi-element antenna arrays capable of beam steering, which helps in directing signals more efficiently toward the intended receiver. This improves both speed and accuracy in data transmission.
Signal processing plays a crucial role in filtering noise and enhancing clarity. Through adaptive algorithms, the system analyzes incoming signals and makes real-time adjustments to improve output quality. This ensures minimal interference even in congested frequency environments.
Additionally, embedded processing units allow continuous monitoring of performance metrics. These units act as the brain of the system, ensuring that adjustments are not only reactive but also predictive. This predictive capability significantly enhances network reliability.
Overall, the architecture is designed to be scalable and flexible, making it suitable for a wide range of applications from personal devices to large-scale communication infrastructures.
How It Enhances Wireless Connectivity
Wireless connectivity often suffers from issues such as signal degradation, latency, and interference. The antennino approach addresses these challenges by introducing adaptive correction mechanisms that optimize signal flow in real time.
One of the key improvements is beamforming technology, which allows signals to be focused in specific directions rather than spreading them uniformly. This increases efficiency and reduces energy waste. It also enhances signal strength for end users, especially in remote or obstructed environments.
Another important enhancement is interference management. By constantly analyzing surrounding frequencies, the system can avoid congestion and switch to clearer channels automatically. This ensures smoother data transmission without interruptions.
Furthermore, latency reduction is achieved through optimized routing and faster signal processing cycles. This makes the system highly suitable for applications requiring real-time responsiveness such as video streaming and autonomous systems.
Antennino in IoT and Smart Devices
The integration of antennino into IoT ecosystems has opened new possibilities for smart device communication. IoT networks rely heavily on stable and efficient connectivity, especially when managing thousands of connected devices simultaneously.
In smart homes, for example, this technology enables seamless communication between appliances, sensors, and control systems. Devices can respond faster and more accurately due to improved signal clarity and reduced interference. This enhances user experience and system reliability.
Industrial IoT environments also benefit significantly. Machines and sensors operating in harsh conditions often face connectivity issues, but adaptive antenna systems help maintain stable communication channels. This improves operational efficiency and reduces downtime.
As IoT continues to expand, antennino-based solutions are expected to play a key role in ensuring scalability and performance across diverse applications.
Applications in Modern Communication Systems
Modern communication systems demand high-speed, low-latency, and highly reliable connectivity. Antennino-inspired designs are being applied in various fields to meet these requirements effectively.
In telecommunications, they enhance mobile network coverage and improve data transfer speeds, especially in densely populated areas. This leads to better call quality and faster internet services for users.
In aerospace and satellite communication, these systems help maintain stable connections over long distances. Their adaptive nature allows them to adjust to atmospheric disturbances and signal delays, improving reliability.
Defense communication systems also benefit from enhanced signal security and robustness. The ability to dynamically adapt to interference ensures secure and uninterrupted communication in critical operations.
Advantages Over Traditional Antenna Systems
Compared to conventional antenna technologies, antennino-based systems offer several significant advantages. One of the most notable benefits is adaptability. While traditional antennas operate on fixed parameters, these advanced systems adjust dynamically to changing conditions.
Energy efficiency is another major advantage. By directing signals more precisely, they reduce unnecessary power consumption. This not only improves performance but also contributes to sustainability in large-scale networks.
Improved signal quality is also a key benefit. With advanced filtering and optimization techniques, users experience fewer disruptions and clearer communication channels. This is particularly important in high-density network environments.
Lastly, scalability makes these systems suitable for future expansion. Whether deployed in small devices or large infrastructures, they can be easily integrated without major redesign requirements.
Challenges and Future Development Scope
Despite its advantages, the development of antennino-based systems comes with certain challenges. One of the primary concerns is complexity in design and implementation. Advanced algorithms and hardware integration require significant expertise and resources.
Cost is another limiting factor, especially in large-scale deployments. High-end components and intelligent processing units can increase overall system expenses, making it less accessible for smaller organizations.
There are also challenges related to standardization. Since the technology is still evolving, establishing universal protocols and compatibility standards remains an ongoing process.
However, the future holds strong potential. With advancements in artificial intelligence, machine learning, and semiconductor technologies, these challenges are expected to diminish over time, paving the way for more widespread adoption.
Conclusion
the evolution of modern wireless systems is being shaped by intelligent and adaptive technologies that redefine connectivity standards. The rise of antennino represents a major step toward smarter, more efficient communication networks capable of meeting future demands.
By integrating advanced signal processing, adaptive architecture, and real-time optimization, this innovation enhances everything from mobile communication to industrial IoT systems. It addresses key limitations of traditional antennas while opening new possibilities for scalable and high-performance networks.
As global connectivity continues to expand, antennino will likely play a crucial role in shaping the next generation of communication infrastructure. Its ability to adapt, optimize, and evolve makes it a foundational concept in the future of wireless technology.
Read More: Cryptoboostly.co.uk
Tech
Metronidasool: Uses, Benefits, and Safety Guide
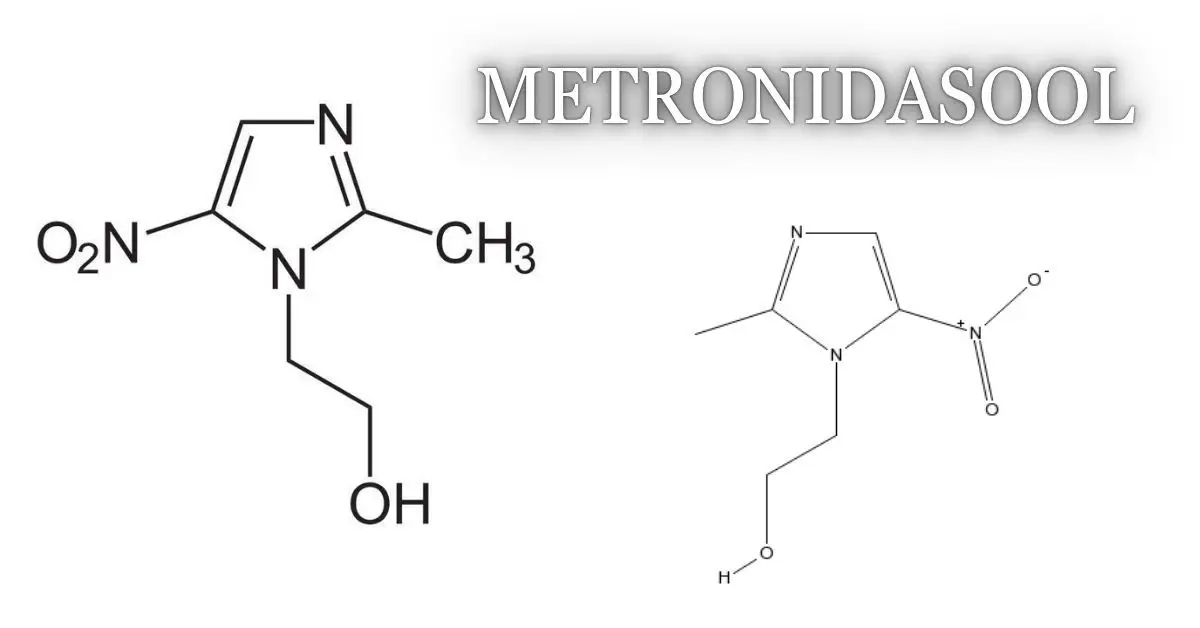
Metronidasool is a commonly referenced spelling variation of metronidazole, a well-known antibiotic and antiprotozoal medication used to treat a wide range of infections. Doctors prescribe it for bacterial infections, dental problems, stomach conditions, and certain parasitic diseases. Because it is both effective and affordable, this medicine has become an essential treatment option worldwide. Understanding how metronidasool works, when it is prescribed, and how to use it safely can help patients get the best results while avoiding unnecessary side effects.
What Is Metronidasool and How Does It Work?
Metronidasool belongs to a class of medicines called nitroimidazole antibiotics. It is designed to kill anaerobic bacteria, which are bacteria that thrive in environments with little or no oxygen. It is also highly effective against certain parasites such as Giardia lamblia, Entamoeba histolytica, and Trichomonas vaginalis. This dual action makes it one of the most versatile anti-infective drugs available.
Once taken, the medication enters the bloodstream and penetrates infected tissues. Inside the harmful microorganism, it interferes with DNA synthesis and damages the organism’s genetic material. Without the ability to repair and reproduce, the bacteria or parasite dies. This mechanism is selective, meaning it targets microorganisms while leaving most human cells unaffected.
Metronidasool is available in several forms, including tablets, capsules, topical gels, vaginal suppositories, and intravenous solutions. This variety allows doctors to tailor treatment based on the type and severity of the infection. Oral tablets are the most common form and are widely used for gastrointestinal, dental, and reproductive tract infections.
The medication is often prescribed when other antibiotics are ineffective because many anaerobic bacteria remain highly sensitive to metronidazole. Its broad spectrum and excellent tissue penetration make it especially useful in treating infections in hard-to-reach areas such as the abdomen, liver, and gums.
Will You Check This Article: Lotus Pose: A Complete Guide to Mastering Padmasana
Common Medical Uses of Metronidasool
Metronidasool is used to treat numerous infections involving different systems of the body. One of its most common uses is for bacterial vaginosis, a condition caused by an imbalance in normal vaginal bacteria. It is also the first-line treatment for trichomoniasis, a sexually transmitted infection caused by a parasite.
In dentistry, metronidazole is frequently prescribed for gum infections, dental abscesses, and severe periodontitis. Anaerobic bacteria are a major contributor to oral infections, and this medication effectively eliminates them. Many dentists combine it with other antibiotics to provide broader coverage.
Gastrointestinal conditions are another important area where metronidasool is widely used. It helps treat infections such as amoebiasis, giardiasis, and Clostridioides difficile colitis. In combination with other medications, it may also be part of treatment regimens for Helicobacter pylori, the bacterium linked to stomach ulcers.
Doctors use metronidazole for skin conditions as well. Topical formulations are commonly prescribed for rosacea, reducing redness and inflammatory bumps. In surgical settings, the drug may be given before and after abdominal procedures to prevent postoperative infections.
Metronidasool for Stomach and Intestinal Infections
Digestive tract infections are among the most common reasons physicians prescribe metronidasool. Parasites like Giardia can cause diarrhea, bloating, and stomach cramps after consuming contaminated food or water. Metronidazole effectively eliminates the parasite and relieves symptoms within days.
Amoebic dysentery, caused by Entamoeba histolytica, can lead to severe diarrhea and abdominal pain. If left untreated, the parasite may spread to the liver and form abscesses. Metronidasool is highly effective against both intestinal and liver infections caused by this organism.
Another critical use is in treating Clostridioides difficile infection, often associated with antibiotic use. This condition can cause severe diarrhea and inflammation of the colon. While newer medications are sometimes preferred, metronidazole remains an option in certain cases.
The medicine is also used in combination therapies to eradicate Helicobacter pylori. By reducing bacterial load, it helps heal ulcers and decreases the risk of recurrence. Patients should always complete the full prescribed course to ensure successful treatment.
Benefits of Metronidasool Compared to Other Antibiotics
One of the greatest advantages of metronidasool is its targeted action against anaerobic organisms and protozoa. Many antibiotics do not work well against these microbes, making metronidazole a uniquely valuable option. Its effectiveness has been proven over decades of clinical use.
The medication is available in generic form, which makes it affordable for patients in both developed and developing countries. Its low cost contributes to its widespread use in hospitals, clinics, and pharmacies around the world.
Metronidasool penetrates tissues exceptionally well. It reaches high concentrations in saliva, vaginal fluids, intestinal tissues, and abscesses. This characteristic allows it to treat infections in locations where other drugs may struggle to reach therapeutic levels.
Another major benefit is its flexible dosing and multiple formulations. Whether the infection requires a topical gel, oral tablet, or intravenous infusion, healthcare providers can choose the most suitable route of administration. This versatility enhances treatment success.
Proper Dosage and How to Take Metronidasool Safely
The exact dosage of metronidasool depends on the type of infection, the patient’s age, and overall health status. Some infections require a single high dose, while others need treatment for 5 to 14 days. Doctors may adjust the dose for patients with liver disease.
The medicine should be taken exactly as prescribed. Tablets are usually swallowed with water and may be taken with food to reduce stomach upset. Skipping doses can reduce effectiveness and increase the chance that the infection will return.
Alcohol should be avoided during treatment and for at least 48 hours after the final dose. Combining metronidazole with alcohol can cause nausea, vomiting, abdominal cramps, and flushing. This interaction is well known and can be quite uncomfortable.
Patients should finish the full course even if symptoms improve quickly. Stopping early may leave some microorganisms alive, allowing the infection to persist or recur. Consistent use is essential for achieving a complete cure.
Side Effects and Drug Interactions to Know
Like all medications, metronidasool can cause side effects. Common reactions include nausea, metallic taste, headache, loss of appetite, and mild stomach discomfort. These effects are usually temporary and improve after treatment ends.
Some patients may experience dizziness or fatigue. Because of this, caution is advised when driving or operating machinery if these symptoms occur. Darkening of the urine can also happen and is generally harmless.
Rare but serious side effects include numbness or tingling in the hands and feet, seizures, and severe allergic reactions. Patients who notice these symptoms should seek immediate medical attention and stop the medication unless instructed otherwise by a physician.
Metronidazole interacts with several drugs, including blood thinners such as Warfarin, which may increase bleeding risk. It can also interact with Lithium and certain seizure medications. Informing your doctor about all current medications is essential.
Who Should Avoid Metronidasool?
Although metronidasool is safe for most people, certain individuals require special caution. Patients with severe liver disease may need lower doses because the drug is metabolized in the liver. Those with neurological disorders should be monitored carefully.
Pregnant women should consult their healthcare provider before using metronidazole, especially during the first trimester. In many situations, the benefits outweigh the risks, but treatment decisions should always be individualized.
Breastfeeding mothers may also need guidance, as small amounts of the medication can pass into breast milk. Physicians may recommend temporary precautions depending on the dosage and duration of therapy.
Anyone with a known allergy to metronidazole or related nitroimidazole drugs should avoid using it. Alternative antibiotics can usually be prescribed if hypersensitivity exists.
Conclusion
Metronidasool is a highly effective medication for treating bacterial and parasitic infections involving the digestive system, reproductive tract, skin, and mouth. Its ability to target anaerobic bacteria and protozoa makes it an indispensable option in modern medicine. With proper use, it can provide rapid relief and prevent complications from serious infections.
To use metronidasool safely, patients should follow dosing instructions carefully, avoid alcohol, and complete the entire course of treatment. While side effects are generally mild, awareness of potential interactions and contraindications is important. When taken under medical supervision, metronidasool remains one of the most reliable and widely trusted anti-infective medications available today.
Read More: Cryptoboostly.co.uk




